After looking at the binary dump for the RF controller I realised that I needed to identify the processor I was dealing with. From what I had read the flash image contains the bootloader followed by the code i was interested in. There may also be some data sections. The first step in figuring out the layout was knowing which STM32 chip I was dealing with.
ST-Link
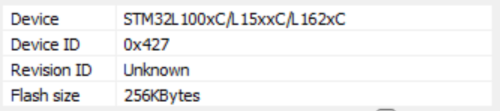
When I grabbed the initial dump ST-Link on Windows 11 didn't have any details of the target available. Attempting to use the newer STMCubeProgrammer on Linux was a total washout as it wouldn't communicate and nothing I could find online helped. Which was a little annoying.
However, going back to Windows 11 I tried St-Link again and this time there was information!
A quick visit to the web and I was soon looking at https://www.st.com/resource/en/reference_manual/cd00240193-stm32l100xx-stm32l151xx-stm32l152xx-and-stm32l162xx-advanced-arm-based-32-bit-mcus-stmicroelectronics.pdf
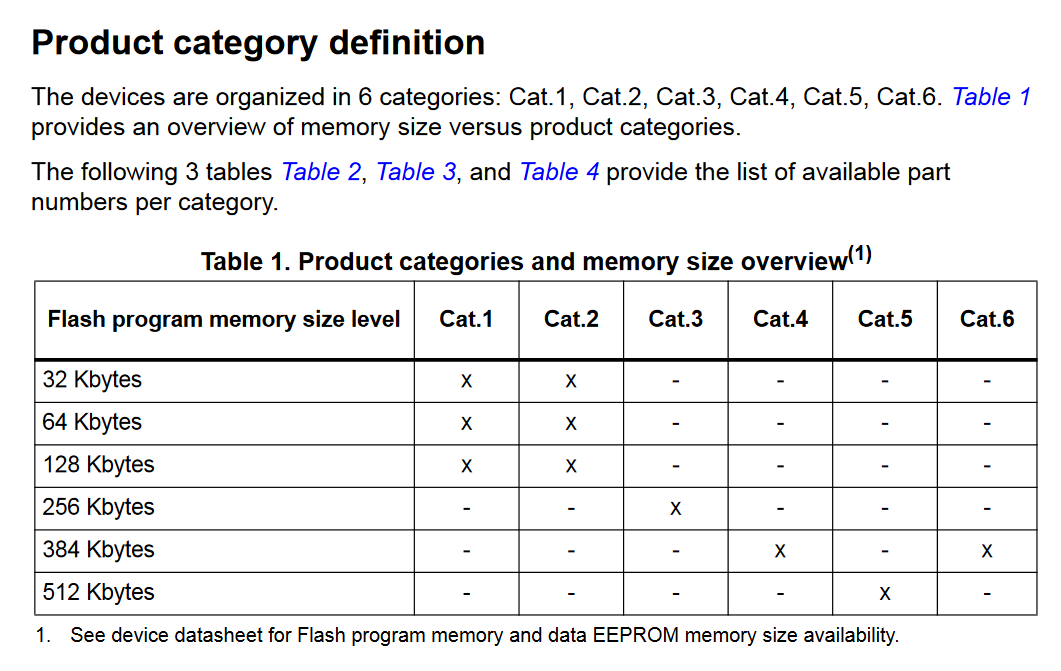
Armed with the information that there is 256Kbytes of flash memory, the product category table makes simple reading.
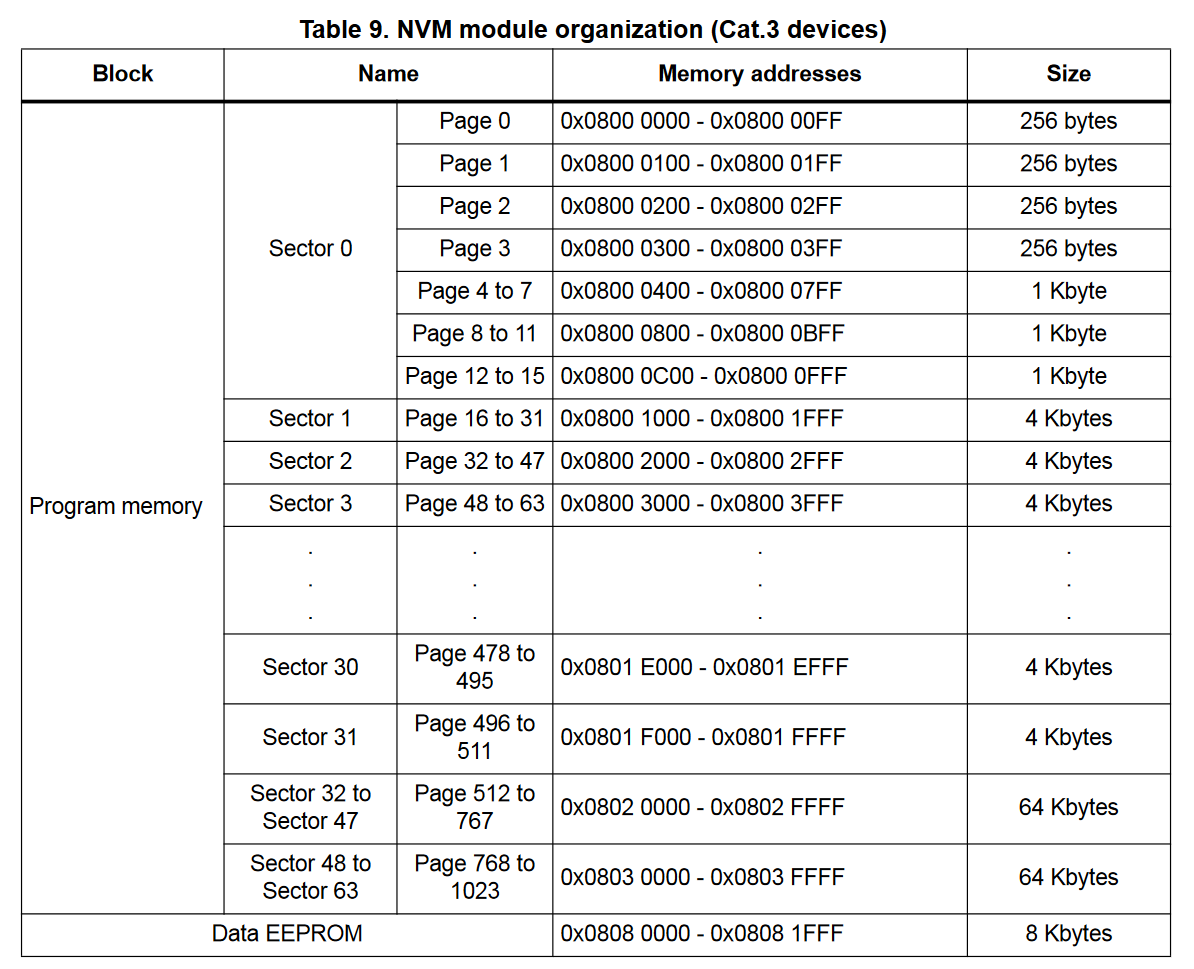
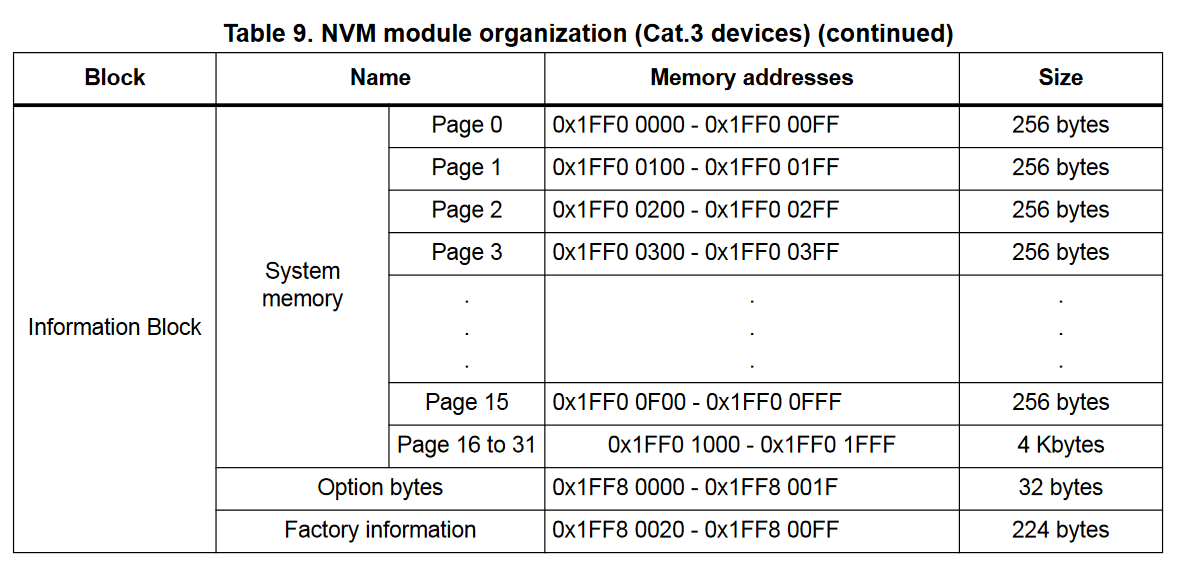
Later in the document the memory configuration for Cat.3 devices is shown.
The other aspect I wanted to confirm was the CPU.
A quick search revealed some Cortex-M3 documentation at https://documentation-service.arm.com/static/5e8e107f88295d1e18d34714?token=
Device ID?
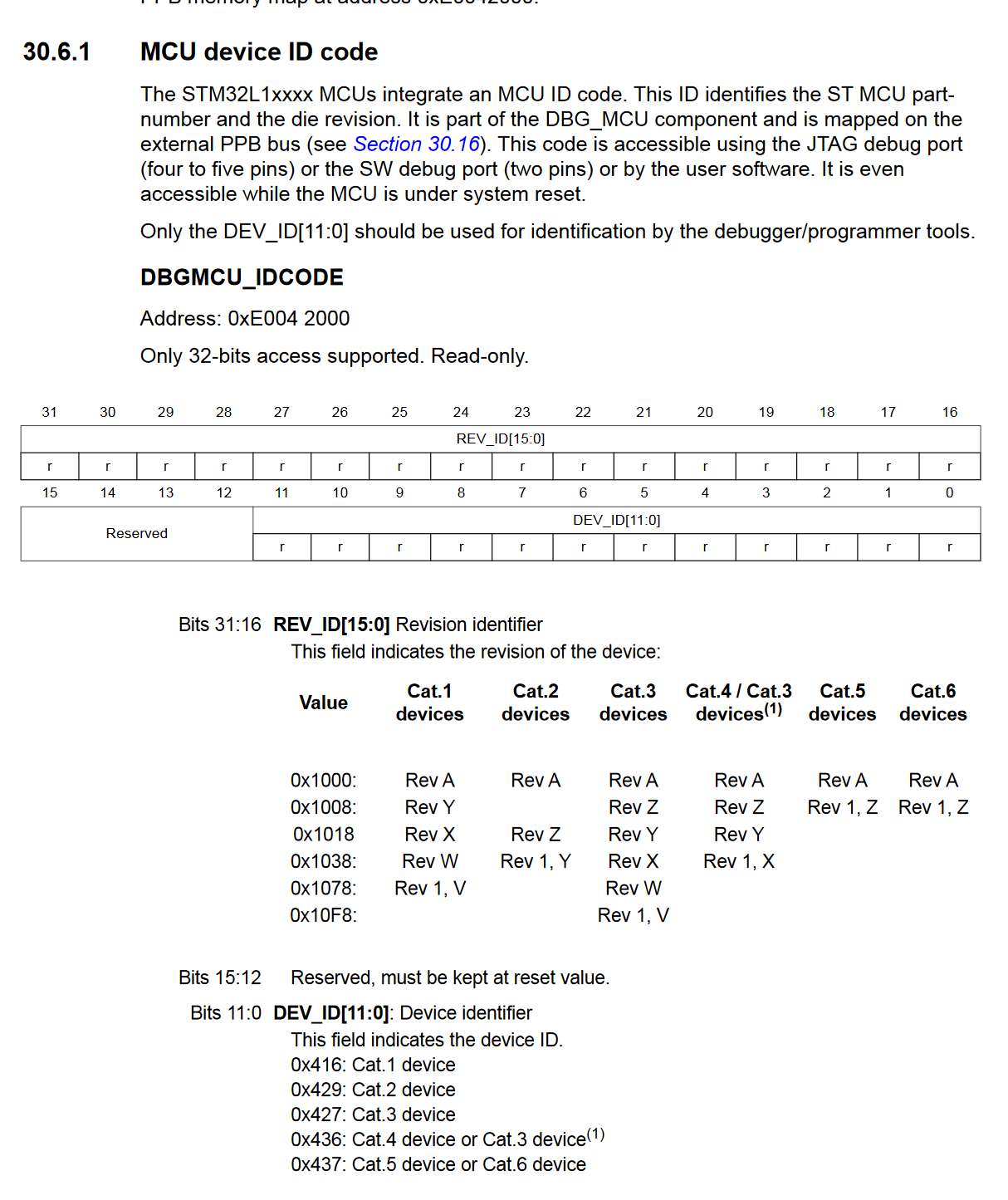
Again, using ST-Link I checked the value @ 0xE0042000 which was 0x10F86427.
This looks to be a Rev 1,V of a Cat.3 device.
Factory Information?
A quick look with ST-Link confirms we have data available.
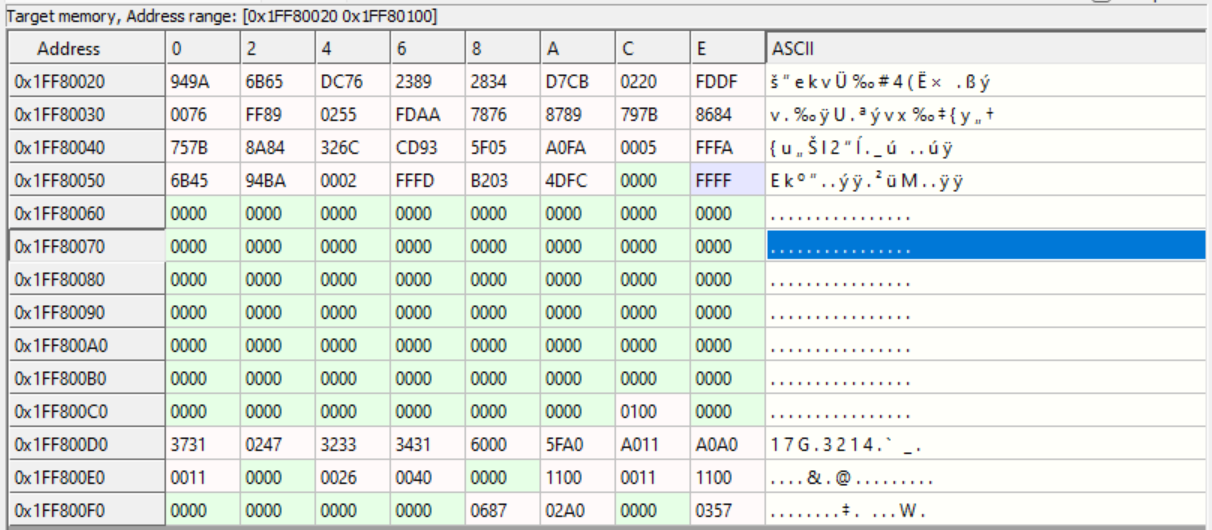
The document doesn't provide a breakdown of what the factory information contains, but it was where it was meant to be :-)
THUMB not THUMB2
Reading some documents about the Cortex-M3 it appears that the instruction set will be THUMB and not the newer THUMB2 that had been assumed by the decompilers I looked at. While they are similar I'm not sure if this will make a difference?
Memory Layout?
Now that I know the memory layout I have dumped the full 256Kbytes into a file to start examining in more detail. I still need to figure out how large the bootloader is and where the actual application code starts. While I can find a lot of online references to writing bootloaders I have yet to find many that detail decompiling them!
If anyone has any links that will help then I'd be grateful if you can send them along.